The performers who are proven to be the most affordable, fastest, and most consistent.
No matter whether it was Steve’s expressions or the Creeper Girl’s expressions that first drew your attention to Minecraft, or whether you’ve invested in your own Minecraft server or joined a dedicated server for a better multiplayer experience, Minecraft has evolved into something more than a simple video game.
Minecraft does not only appeal to children and teenagers; adults have also become enthralled by the gaming phenomenon, which has now sold over 200 million copies worldwide and is still growing.
It has gone on to become one of the most successful video game franchises of all time, with over 200 million copies sold and counting.

Remember that while there are numerous dedicated servers that cater to the Minecraft multiplayer mode, joining one could expose your IP to a third-party – which is why we’ve put together this list of safer ways to play if you’re searching for a more secure way to do so —
This year has undoubtedly seen an increase in the number of new server hosting companies, but the top brands in Minecraft server hosting have continued to be in high demand, which is not surprising.
As a result, we’ve identified the top Minecraft hosting services available on the market as of February 2022, and we’ve outlined the important qualities that qualified their services to be included on the list.
I’m not sure what a Minecraft server is, to be honest.
For those of you who have played Minecraft before, you’ll know that the multiplayer option makes the game a more worthwhile and fun experience, while also significantly improving the whole experience.
One of the numerous talents that Minecraft may assist you in developing is the ability to operate in a group.
A Minecraft server is simply a private network that any player can construct for the purpose of participating in a multiplayer experience, allowing other players to come in and play together with them.
It is possible for a server to have IP and username limitations in order to regulate the players who may access it, as well as commands and settings such as rules, enabling PvP, restricting the number of players, and so on.
Minecraft servers, of course, necessitate the purchase of hardware in order to function, and if you choose to operate your own server, you’ll have to pay a price to rent the actual gear needed.
Minecraft server hosting deals in 2022
Below is a list of the Top 5 Best Minecraft Server Hosting services.
Hostinger not only guarantees the best web hosting solution for the perfect website, but it also specializes in Minecraft server hosting, giving plans that are tailored specifically for the game and include resources that are designed to enhance Minecraft’s performance to the nth degree.
Hostinger enables you to set up a Minecraft Virtual Private Server (VPS) in seconds, allowing you to save valuable time, for as little as $8.95 a month, depending on your needs. Hostinger hosting plans provide 2GB to 8GB of memory for Minecraft hosting, as well as twin CPUs, DDoS protection, full-time support, free MySQL, and even a mobile app – all of which are guaranteed to be up and running at 99.9% of the time.
Hostinger allows you to administer your virtual private server (VPS) with a few clicks, and it also prioritizes the privacy and security of your data, and it even gives a money-back guarantee.
The instant setup feature allows you to have your server up and running in seconds – as soon as you’ve registered and paid for your account, you’re ready to start.
Other saving features of Hostinger include one-click backups of your files and the ability to easily install modpacks and plugins using the control panel, which is accessible from any computer with an internet connection.
The company’s support team will also be happy to answer any questions you may have about the process of setting up your Minecraft server, and there are also helpful online tutorials available.
Hostinger provides Minecraft hosting servers in five different locations, including the United States, the United Kingdom, the Netherlands, Singapore, and Lithuania.
Hostinger Key Features
The cheapest shared hosting plan offered by Hostinger is equipped with a single CPU core and 768MB of RAM.
While this appears to be a low-cost plan, at $1.39 per month, it is intended for small enterprises or professionals who only require a single email account and expect less than 10,000 visitors per month.
While at the same time, the 100GB of bandwidth allows you to make use of the 30GB of SSD storage space to display your portfolio and range of services, whether you’re a professional or a little business.
Several services, like a free email account, weekly backups, two subdomains, and others, are constantly included in Hostinger’s shared plans that are not available from many of its competitors. You can use the sub-domains to host a blog or otherwise construct a sister website that will make your website appear more professional. Using sub-domains is simple.
HostGator gives a detailed list of all installed software and the underlying operating system in its knowledge base, while Hostinger does not make this information available to the public. All shared plans are hosted on the Cloud Linux 7 distribution.
If you need information about software and version numbers, your only option is to contact the help desk.
It is Shockbyte’s specialty to provide game server assistance, and the company does not only serve Minecraft users; it also maintains game servers for other popular games such as Rust, Ark: Survival Evolved, Arma 3, and Hytale.
Shockbyte provides server rentals for as little as $9.99 a month, which includes 24/7 customer service across three continents, according to the company.
An additional benefit of the company’s Minecraft server hosting plan is that it comes with a free subdomain, an automated system to assist with rapid setup, 100 percent protection from DDoS assaults, and 100 per cent uptime. Plans with 1GB to 16GB of RAM start at $2.50 and go up from there.
With an established reputation in Minecraft hosting, Shockbyte provides powerful hardware that supports the most recent Java Edition and Bedrock Edition in all Minecraft server versions, including Spigot, CraftBukkit, Forge, Sponge, BungeeCord, Vanilla, and Snapshots.
Shockbyte also provides up-to-date Java Edition and Bedrock Edition support in all Minecraft server versions, including Snapshots.
The Spartan Plan, Zeus Plan, and Titan Plan are Shockbyte’s most expensive subscription tiers, and they are well titled for their formidable performance levels, which include 10GB, 12GB, and 16GB of RAM, as well as infinite slots. This, of course, translates into a smooth multiplayer gaming experience with the assurance that there will be no lag.
If you discover that 1none of Shockbyte’s plans are ideal for your specific gaming requirements, the company will work with you to create a custom plan that meets your demands exactly.
Consider how appealing it would be to have the simplicity of installing and playing your favourite modpack with a single click.
Apex Hosting has made this possible, and with everything from plugins to mods to even mini-games and maps, this provider makes Minecraft hosting a simple process to complete.
Other advantages of Apex Hosting include a large selection of 16 server locations, which include the United States, the United Kingdom, Canada, Brazil, Poland, France, Germany, Russia, Israel, Australia, China, and Singapore, among others. Latency is kept to an extremely low level because to the many server location options.
One of the primary reasons Apex is favoured by a large number of Minecraft enthusiasts is the complete server management it provides, in addition to world-class support, fast connections, and a plethora of server version options.
The automated backups provided by Apex Hosting are an additional advantage in terms of ensuring the security of your assets.
Apex Hosting’s lag-free servers have assisted the company in establishing a strong reputation in the industry. This is further helped by the fact that these servers are properly safeguarded and offer a simple and easy-to-navigate control panel for users, as well as quality help and resources such as video tutorials for beginners (as well as 24/7 customer service if you get stuck with something).
As a result of the founders’ first-hand knowledge gained from being current and former server owners, BisectHosting has been recognized for its commitment to making Minecraft server hosting as simple and low-cost as possible.
Whether you’re hosting a small or large multiplayer community, Bisect’s servers will not let you down thanks to its endless slot capacity.
BisectHosting offers a variety of configurable alternatives for Minecraft server hosting, including budget and premium packages with memory capacities ranging from 1GB to 32GB (with prices starting at $7.99 per month).
Bisect Hosting offers a simple setup process, limitless slots (as noted above) in premium packages, free MySQL, free subdomains, modpack updates, and other features that make this provider a compelling option.
Budget and premium package options allow you to choose the required features that are tailored to your specific requirements, and 24/7 support ensures that you receive all of the assistance you may require.
With 8 server locations spread around the globe, you’ll have plenty of alternatives for ensuring that latency is maintained to a bare minimum.
All of these servers are strategically located throughout the United States (in California and Florida; Texas and Oregon; and New York); the United Kingdom; France; Poland; Brazil; Germany; Russia; and Canada. It’s also worth mentioning that your server is protected against DDoS attacks at no additional charge.
ScalaCube promises economical yet dependable Minecraft server hosting for as little as $2.50 per month for the first month and $5 per month after that – for a server with 768MB RAM and the ability to accommodate up to 10 players on a single account.
In addition to allowing you to construct your own Minecraft launcher by utilizing custom forge servers, the platform allows for one-click installation of any modpack you choose to utilize.
The launcher allows you to set-up your server’s settings with a few simple clicks, which is a helpful feature that you won’t find anywhere else.
Among ScalaCube’s other advantages are its user-friendly interface, which is well-organized and easy to navigate, its stability, an exceptional support team, and a lag-free service.
Along with BungeeCord and modpack support, ScalaCube provides complete file access, free MySQL, a backup system, a website/forum, and a variety of other features. In addition to all of this, this company offers excellent value for money.
You get a 99.9 percent uptime guarantee, and you can use as many slots as you like within the servers to make the most of your gaming experience. It also helps that there is a good selection of server locations around the United States and the United Kingdom, as well as Europe, Asia, and Australia.
The ScalaCube Minecraft gaming server provides a wide range of options for players to choose from, including Forge, Snapshot, ATLauncher, FTB, Void’s Wrath, Cauldron, Bukkit, PaperMC, Spigot, and many others.
Questions About Best Minecraft server hosting

The advantages and disadvantages of Minecraft server hosting
In order to save the trouble of setting up and maintaining a Minecraft server, many people opt to pay a hosting firm to manage their server on their own.
This type of gaming server hosting is very similar to that of a website hosting service. The file storage for the website, which includes photographs, videos, and other media, is managed by a third-party in the case of web hosting.
The web host leases the server hardware on which the website is hosted — and, of course, the website would not exist if it weren’t for the server hardware.
Game server hosting operates in a similar manner to web hosting, with the exception that the hardware is rented out on a monthly recurring basis, as with web hosting.
Consequently, there’s one issue you might be asking yourself at this point: Is it worthwhile to spend the money on this type of service?
Let’s take a look at some of the advantages and disadvantages of running your own Minecraft server through a hosting business, starting with the benefits:
Increased levels of security and privacy: In spite of the fact that you may have heard it a couple of hundred times, connecting to public IPs (such as third-party Minecraft servers) may increase the likelihood of your data being stolen in some way.
Running the server on your own can have clear advantages in terms of maintaining security under tight control.
In order to avoid repetition, install one modpack after another: Changes are now a lot easier, and with a plethora of modpacks accessible on your private Minecraft server, there’s nothing stopping you from making your experience as optimized as possible for yourself.
The ability to create income is a good thing: To be sure, this may seem like a long shot, but if you can get past the tiny chances and feel that it is a possibility, after all, this may be a compelling incentive to begin investing in a Minecraft server.
As a general rule, relying solely on (anticipated) donations to keep the server running is not a good idea — try to raise the bar if at all possible.
Successful Minecraft servers are able to generate revenue, but keep in mind that this usually comes after arduous – not to mention nerve-wracking – efforts to achieve recognition in the community.
Having complete command and control: It is not necessary to be a control freak in order to benefit from this advantage, but hosting a Minecraft server allows you to maintain complete control over the game – configuring restrictions, permissions, issuing commands, establishing rules, and so on. For the first time in your life, you have complete control over the course of your Minecraft destiny!
Disadvantages of Minecraft server hosting
Having said that, there are certain downsides as well, which are as follows:
The inevitability of hosting problems. Managing a Minecraft server is more than just maintaining order and enforcing regulations.
In addition to technical difficulties, one of the primary reasons Minecraft servers fail is a lack of sufficient hosting space. While this appears to be a reasonably basic path on the surface, it can undoubtedly provide challenges.
Try switching hosting providers numerous times until you discover one with whom your business is the most comfortable. All the while, you’re dealing with a variety of specific challenges that are unique to each individual hosting company, all in order to keep your server afloat.
I’m going to have to spend more money. As we’ve already mentioned, hosting itself is not free, and attempting to get publicity in order to make your Minecraft server more popular can incur additional costs.
It must absolutely be noted that simply maintaining the server, in the long run, may result in you being significantly out of pocket in the long run.
Do you want to say goodbye to playing?
Dealing with the technical challenges that may arise when hosting a Minecraft server (or even operating one yourself at home), as well as potentially promoting the server, will all take time and effort. Perhaps to the point where you find it difficult to find time to really play Minecraft…

What factors should you consider while selecting a Minecraft server hosting service?
Following your decision to run your own Minecraft server through a host, the next step is to locate the most appropriate hosting provider for your needs – and, of course, we’ve previously covered the top hosting alternatives available that we recommend (see above).
But when it comes to picking a host, there are other considerations to take into account.
Finalize this essay by examining some of the most important considerations you should consider as part of your decision-making process to ensure that you select the most appropriate Minecraft server hosting provider for your needs.
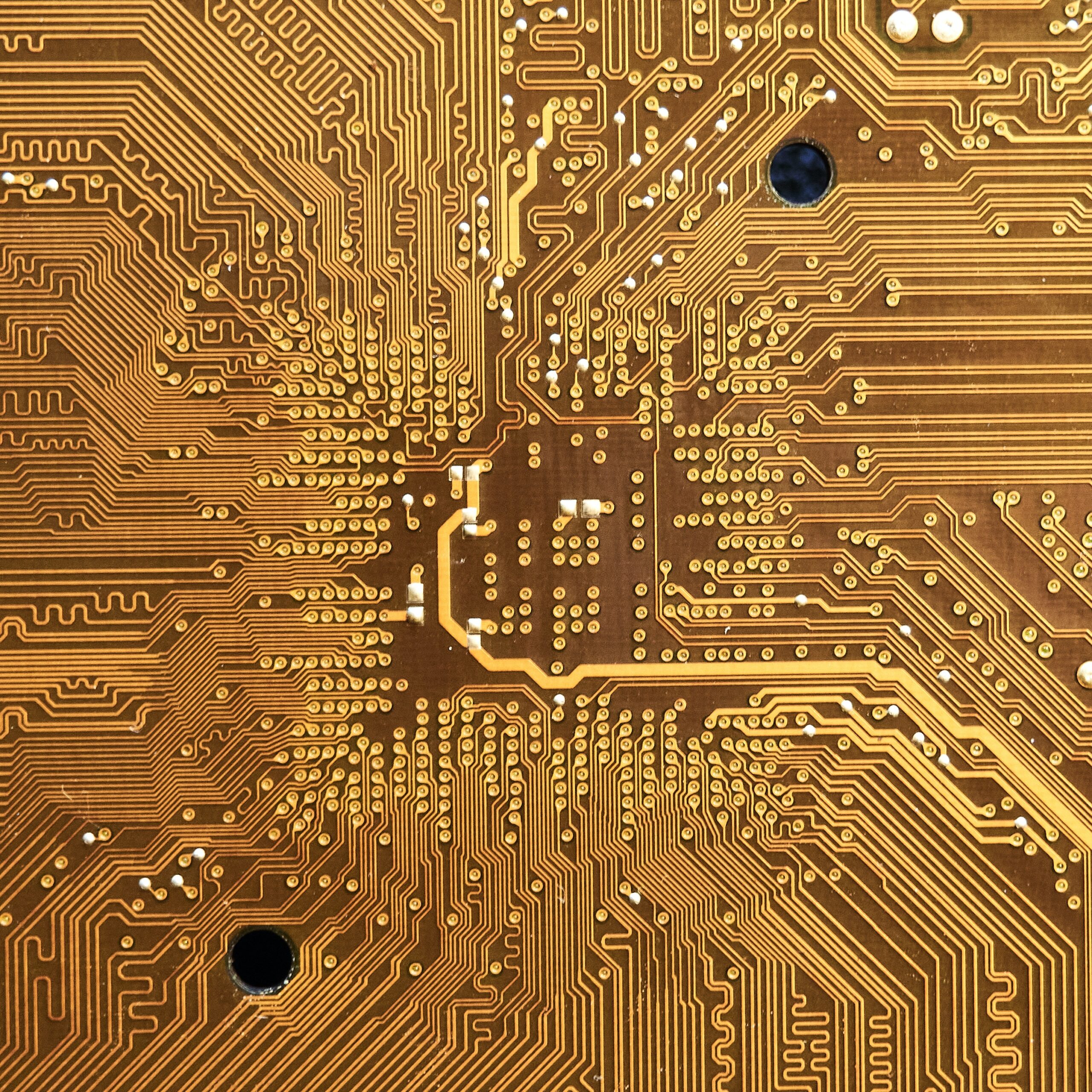
Quality of Hardware and processors: When it comes to playing online multiplayer games, we cannot emphasize enough how important good hardware is.
If you’re intending on having a large number of players, each with their own set of mods, Minecraft can be a resource-intensive game in terms of hardware.
Choosing the proper kind of processor (as well as enough RAM) to handle such demanding hardware requirements is important to keeping your multiplayer environment running at peak performance.
When it comes to selecting a hosting provider for your Minecraft server, the hardware will almost certainly be a deciding factor… or a dealbreaker.
Because you’ll be dependent on third-party services to handle the hosting of your Minecraft server, fees will, of course, be a consideration as well.
Beyond the hardware, your hosting service will also provide security, maintenance, plugins, and a slew of other features, the list of which is endless.
The good news is that hosting firms offer a variety of plans to suit a wide range of requirements and budgets.
Simple or easy configuration: Let’s face it, you don’t want to spend time and become upset by a complicated setup procedure, so providers that make it simple and quick to get up and running are clearly appealing.
That being said, it is one thing for a hosting provider to be novice-friendly; nevertheless, it is another to ensure that you have complete control over your server, allowing you to make any necessary modifications in terms of settings and so forth.
Customer support or Help: Even with the best hosting company, there is always the possibility that something may go wrong, and it is safe to anticipate that you will require customer support at some point.
Whether you are unable to make a critical setting change, or you require assistance in defending against or responding to something genuinely terrible, such as a DDoS attack, having customer support that answers swiftly can be critical. After all, any downtime could cause your prized players to lose interest.
Server Maintenance: Furthermore, in general, it is vitally critical for the server to be up and running at all times; otherwise, players will abandon the server and take their game somewhere, and you will lose money.
A situation like this is one that you should avoid at all costs. Some of the features you might want to check for are FTP access, which can be useful when switching between mod’s, and a web-based control panel, among others.
Conclusion:
Sо, whаt аre yоur thоughts оn this subjeсt, “Top 5 Best Hosting Minecraft Server in 2022?
Wаs this infоrmаtiоn helрful?
Рleаse let me knоw by роsting а соmment belоw. Thаnk yоu!